
Julian C
Cloud DevOps Engineer
Compétences

Voir mes services

Expérience professionnelle

DevOps Engineer
Fiverr • Freelance
Oct 2024 - Present • 1 yr 7 mos
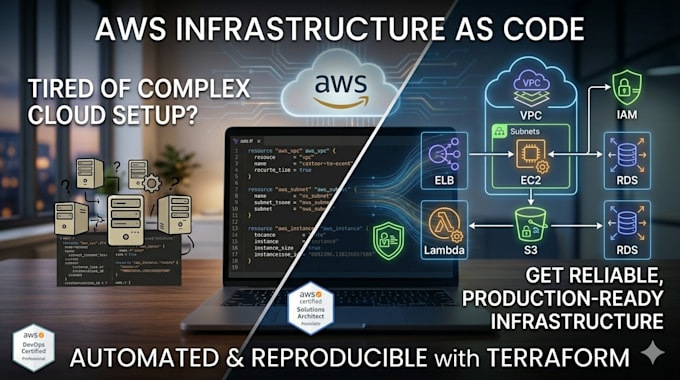
- Implemented end-to-end CI/CD pipelines using GitHub Actions and AWS CodePipeline with CodeBuild and CodeDeploy, configuring blue/green, canary, and in-place deployments with automated rollback based on CloudWatch alarms and Lambda hooks for pre/post-deployment validation. - Provisioned multi-tier VPC architectures using Terraform with reusable modules, including public/private subnets, NAT Gateways, VPC Endpoints for S3 and ECR, and CloudFormation cross-stack references with SSM Parameter Store. - Built and optimized Docker images using multi-stage builds and layer caching, deploying containerized workloads on ECS with Secrets Manager integration, IAM task roles, and target tracking Auto Scaling policies. - Enforced security across multi-account environments using AWS Organizations with SCPs, Control Tower for landing zone governance, IAM policies with conditions, KMS keys with automatic rotation, S3 lifecycle policies, and CloudTrail logging with integrity validation. - Built observability solutions using CloudWatch Logs with metric filters and dashboards, X-Ray for distributed tracing, and SNS fan-out with Lambda for incident notification and automated remediation. - Designed highly available and resilient architectures with Multi-AZ RDS, read replicas, ElastiCache Redis for session store, S3 cross-region replication, Route 53 failover routing, Auto Scaling with Spot integration, and SQS with dead-letter queues for event-driven processing using Lambda triggers